Core Topology & Routing
Abandonment of flat network designs in favor of strict logical segmentation using VMware (Bridged Mode) and NGFW.
- Zone 1 (SOC Network - 10.10.10.0/24): Hosting the SIEM brain (Ubuntu + Wazuh Manager v4.8) and injected attacker infrastructure (Kali Linux) for compromise simulations.
- Zone 2 (Corporate Network - 10.20.20.0/24): Victim environment consisting of a Domain Controller (Windows Server 2022) and mixed corporate endpoints (Windows 10 Pro and Ubuntu Desktop).
- Architectural Milestone: Inter-VLAN routing configuration in FortiGate, disabling NAT between the SOC and Corporate Networks, guaranteeing absolute traceability of attacker source IPs in SIEM logs.
Defensive and Offensive Pillars
Active Directory Hardening
Creation of enterprise GPOs to enable kernel-level auditing (Event ID 4625/4624 and 4688) mitigating LotL techniques. Strict NTP synchronization configuration to protect Kerberos cryptography.
Multi-platform Visibility (XDR)
Unified deployment of Wazuh agents with 100% coverage. Activation of the Vulnerability Detector module to cross-reference endpoint software with the global NIST CVE database. Centralized ingestion of perimeter telemetry by sending NGFW (FortiGate) logs via Syslog to the SIEM to correlate network-level attacks.
Privileges and Zero Trust
Implementation of Microsoft LAPS for automated local credential rotation. Application of Zero Trust on the endpoint via AppLocker, blocking kernel-level binaries with digital signature rules (Publisher Rules).
Hybrid Identity and PAW
Ubuntu integration into AD via realmd/SSSD. Deployment of Windows Admin Center in Gateway mode operating as a Privileged Access Workstation (PAW), protecting the DC without interactive exposure (Pass-the-Hash mitigation).
Custom EDR & Threat Intelligence
Multi-platform development and deployment of the "Security Coach" extension via GPOs and IIS. Ingestion of custom logs in Wazuh by creating proprietary decoders and XML rules, mapping Phishing alerts directly to the MITRE ATT&CK framework (e.g., T1566, T1584).
Red Team Simulation (T1110)
Event pipeline validation operation. Bypass of NLA restrictions and execution of massive dictionary attacks against the Domain Controller's SMB protocol using NetExec.
Active Threat Hunting
Isolation of attack events in the Wazuh dashboard using KQL/Lucene queries, confirming the correct tactical attribution to the Red Team's source IP.
Laboratory Evidence (Attack vs Defense)
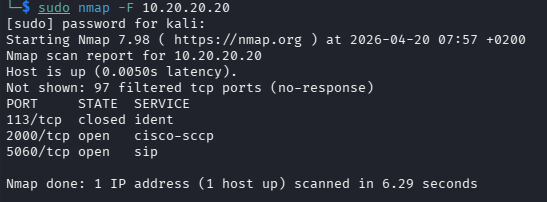
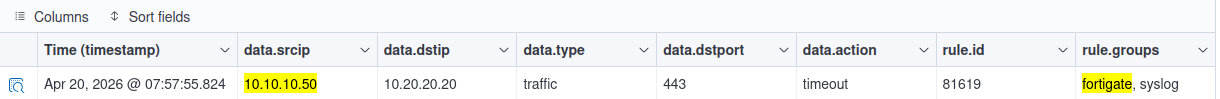
XDR Correlation: Network Reconnaissance (T1595)
Perimeter telemetry verification: On the left, execution of a fast port scan from the attack infrastructure (10.10.10.50). On the right, the SIEM instantly captures and indexes the dropped traffic reported by the FortiGate firewall via Syslog, validating inter-VLAN visibility without NAT masking.
Case Study: SMB Brute Force (T1110)
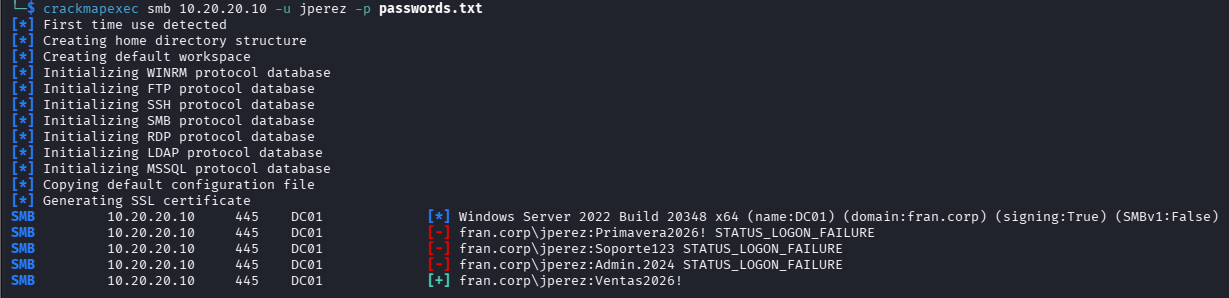
Offensive Execution
Dictionary attack simulation against the Domain Controller's SMB protocol (10.20.20.10) forcing the 'jperez' user with network tools.
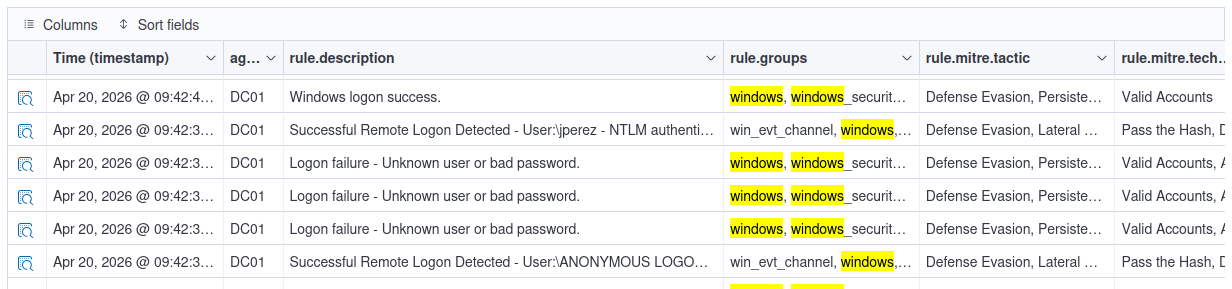
Raw Detection (XDR)
Event isolation in Wazuh Discover. Traceability of the failure cascade (Logon failure) and the final success, mapped to Valid Accounts tactics.
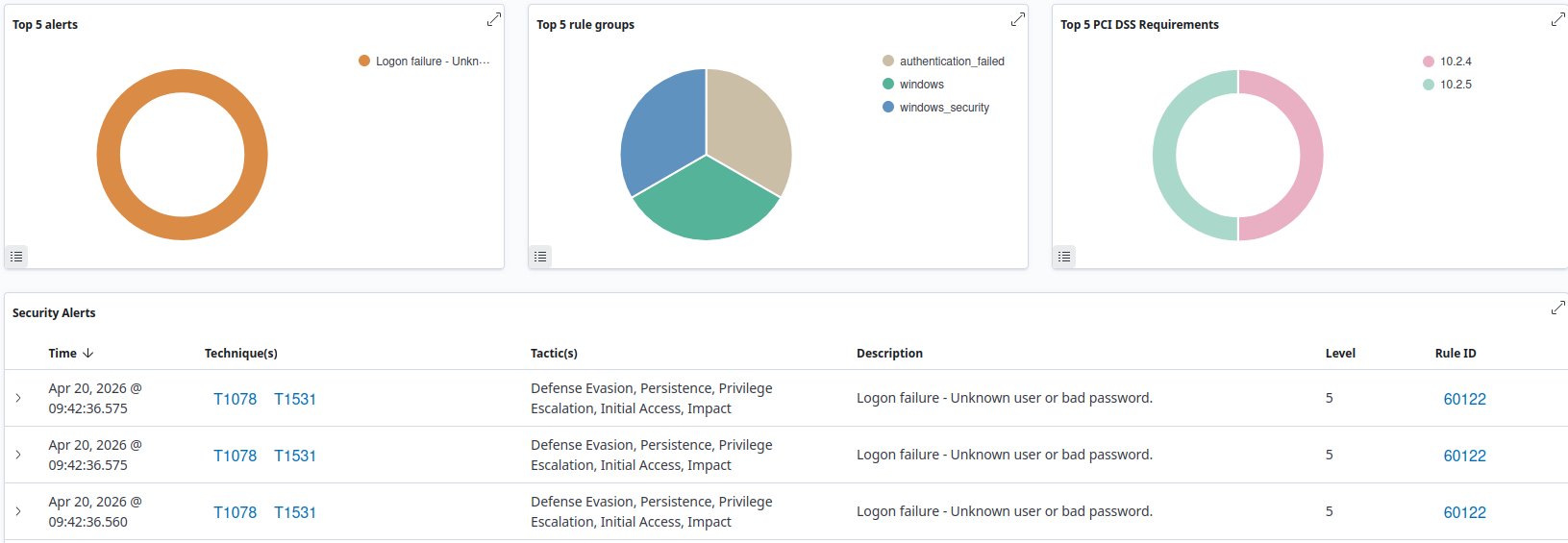
Strategic Intelligence
Translation of logs into executive metrics, showing the impact on PCI DSS compliance requirements (10.2.4) and the top security alerts.