System Architecture
- Frontend Sensor (EDR): Compiled extension (.crx) developed with HTML/JS and Manifest V3. Interacts with the browser's Main World via API Hooking for physical DOM interventions (e.g., disabling password inputs).
- Backend Engine: Asynchronous API developed in Python using FastAPI and Uvicorn for telemetry ingestion and analysis with near-zero latency.
- Corporate Deployment (GPO): Administration via ADMX templates in Active Directory and the
ExtensionInstallForcelistpolicy for forced installation, served through a local IIS.
Advanced Detection Engine & Operations
Heuristic Anti-Phishing
Implementation of the Levenshtein distance algorithm to identify typographical spoofing (Typosquatting) in real-time, coupled with anti-homograph protection (Punycode).
Zero-Trust & k-Anonymity
Integration with HaveIBeenPwned using the k-Anonymity model (sending only the first 5 characters of the local SHA-1 hash) to guarantee the privacy of entered credentials.
Global Threat Intelligence
Real-time integration with the Google Safe Browsing API. On-the-fly evaluation of URLs against global databases for the preventive blocking of infrastructures categorized as Malware.
Domain Intelligence (WHOIS)
Automated queries to extract the Creation Date. Proactive detection and blocking of Newly Registered Domains (NRDs), a critical IoC in ephemeral campaigns.
DLP & Exfiltration
Local mathematical validation (Luhn Algorithm) and preventive copy/paste blocking in sensitive fields to prevent bank card exfiltration.
HSTS / CSP Auditing
On-the-fly HTTP header inspection. Blocking of credential captures on sites without strict encryption policies or cross-site scripting (XSS) mitigation.
Data Masking & Privacy
Automated sanitization using Regular Expressions (Regex) to censor PII and tokens in GET parameters prior to local storage, complying with GDPR regulations.
ChatOps & Resilience
Sending webhooks via Telegram to alert the SOC of critical incidents. Includes a "Kill Switch" for destroying compromised tabs and Anti-DoS Rate Limiting on the backend.
SIEM Integration & Threat Hunting
Telemetry flows into Wazuh in structured JSON format. A custom rule dictionary (IDs 100100 to 100113) was designed, mapping alerts directly to the MITRE ATT&CK framework:
Deployment and Integration Evidence
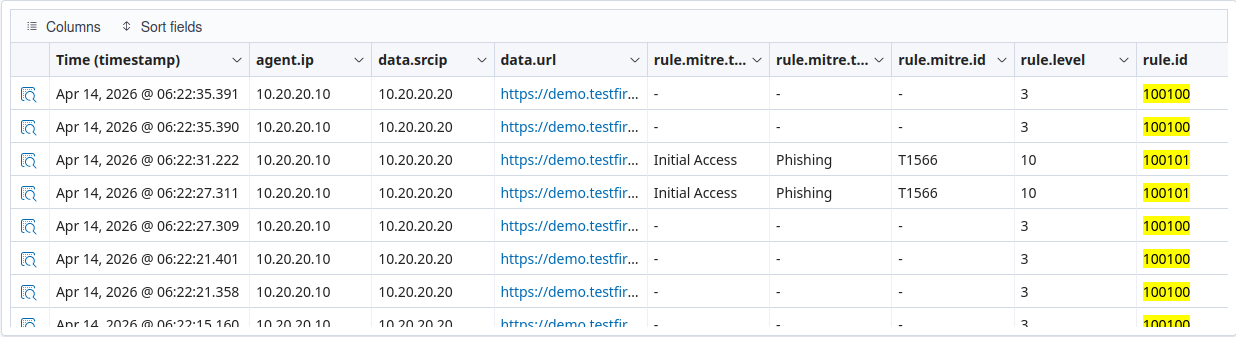
SIEM Integration (Wazuh)
Custom rules (100100/100101) ingesting EDR telemetry and mapping Initial Access tactics (T1566) in real-time.
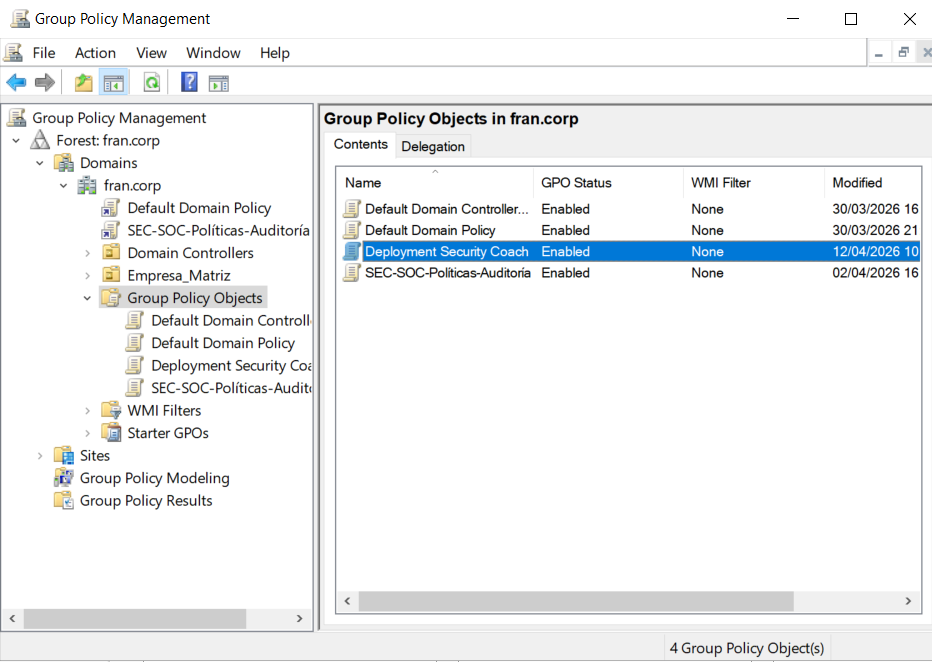
Corporate Deployment (GPO)
Active Directory administration forcing the irreversible installation of the agent on endpoints via group policies.
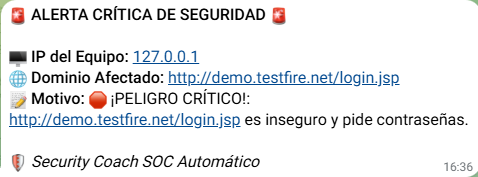
SOC Notifications (ChatOps)
Automated webhook sent from the FastAPI backend alerting the response team to a critical login over plain HTTP.

Frontend EDR Sensor
Agent control panel in the browser processing over 25,000 heuristic detections and monitoring password health.
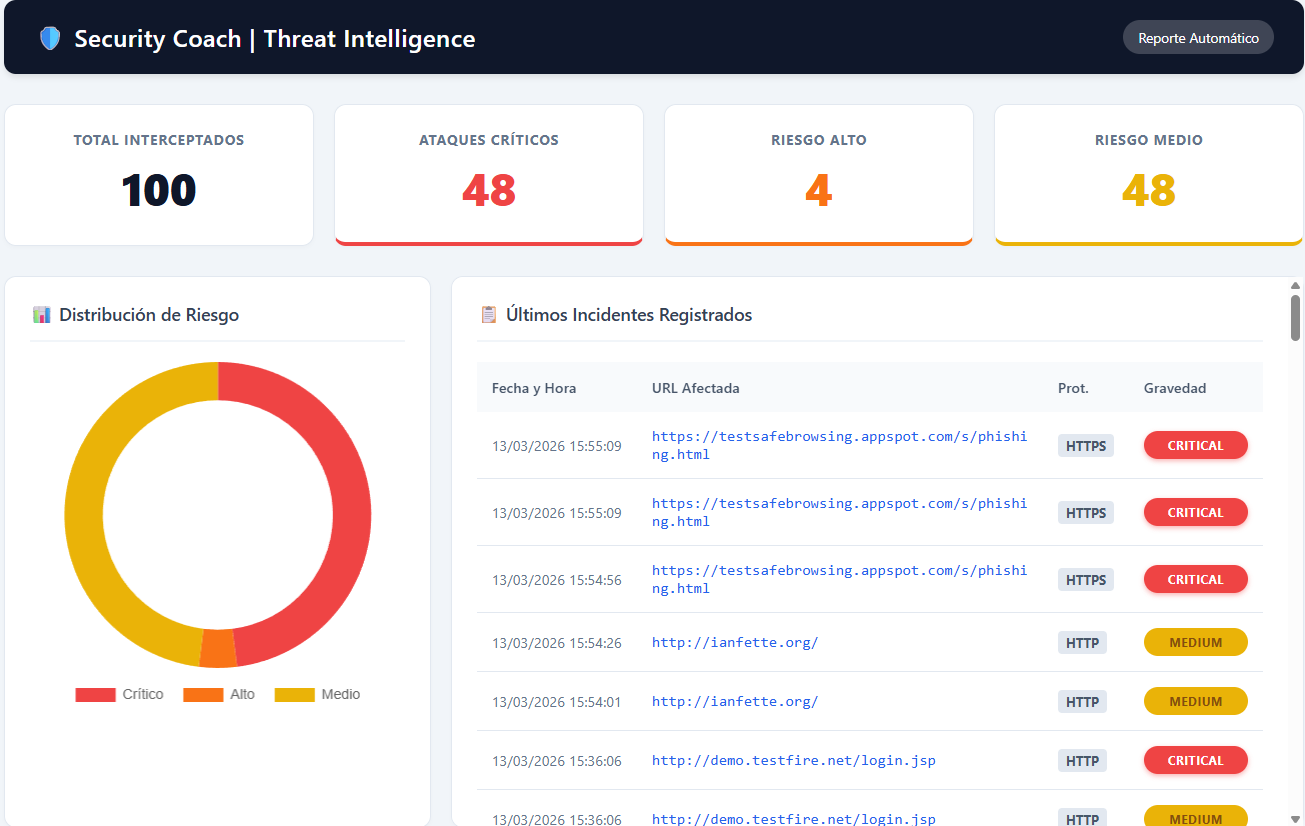
Threat Intelligence Dashboard
Executive control panel dynamically generated from the backend, showing interception metrics, risk distribution, and incident history.

Active Interception (Zero-Trust)
Real-time blocking and alert triggered in the DOM after validating the truncated credential hash against the HaveIBeenPwned API (k-Anonymity).