OpenSentry (Autonomous SOAR)
Open Source Security Orchestration, Automation, and Response.
Overview
Backend design and development of OpenSentry, an autonomous SOAR platform built from scratch. It acts as the central "brain" of a security operations team, exposing a REST API capable of ingesting standardized alerts from any SIEM, enriching them with external threat intelligence, and executing containment actions in firewalls and active directories, reducing the Mean Time To Respond (MTTR) from hours to seconds.
Product Tech Stack
- Core Engine: Python (Flask, SQLite, Requests)
- Automation: PowerShell, WinRM, Telebot
- Endpoint & SIEM: Wazuh API, Sysmon
- Intelligence: MITRE ATT&CK, RegEx
- Integrations: FortiOS API, VirusTotal, AbuseIPDB
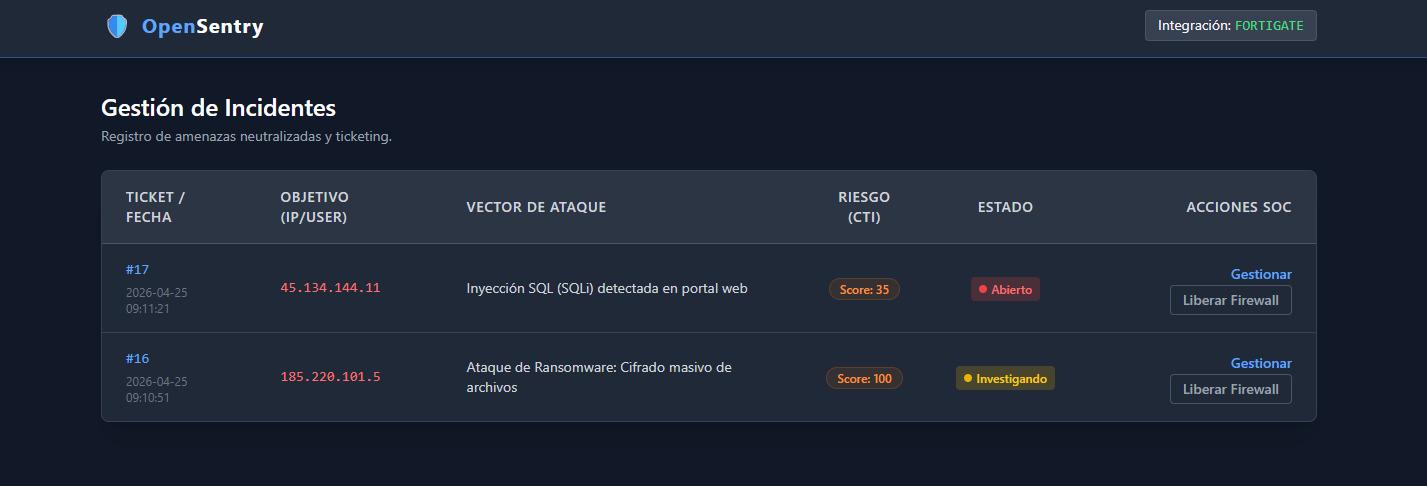
Native web dashboard (Case Management) connected to SQLite.
Core Architecture (Perimeter & Identity)
1. Standardized REST API Ingestion
OpenSentry features an agnostic engine that receives webhooks in JSON format. It evaluates threats based directly on the MITRE ATT&CK framework tactics, allowing integration with any SIEM on the market without relying on volatile text descriptions.
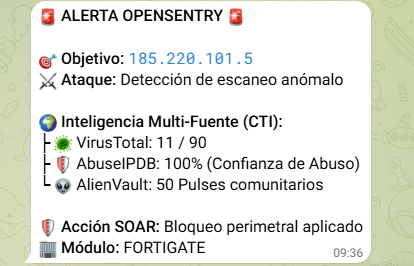
2. Threat Intel Multiplexer (CTI Triad)
Asynchronous enrichment system. Before executing an action, the SOAR triangulates the attacker's reputation by simultaneously querying multiple sources (VirusTotal, AbuseIPDB, and AlienVault OTX), calculating a unified Risk Score to prevent false positives.
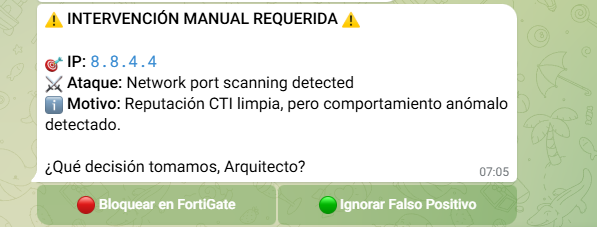
3. ChatOps (Human-in-the-Loop)
For ambiguous or low-confidence threats, the platform suspends automatic execution and requests human authorization via an interactive Telegram Bot, balancing automation with analyst judgment.
EDR Module: Comprehensive Endpoint Protection
OpenSentry incorporates a DevSecOps module designed to act with surgical precision. It functions as the "muscle" of the SOC, evaluating SIEM alerts and executing containment actions in milliseconds using a dual engine that neutralizes both known threats and Zero-Days.
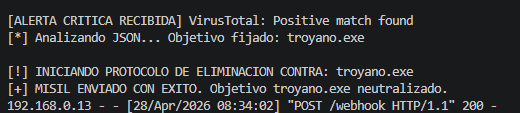
🛡️ Active Elimination Engine
Based on Threat Intelligence. The system intercepts the execution of new processes at the Kernel level (Sysmon). The SOAR cross-references the cryptographic Hash with VirusTotal. If confirmed as malicious, it dynamically extracts the executable's name and orders the agent to immediately annihilate the process, regardless of how the attacker disguised it.
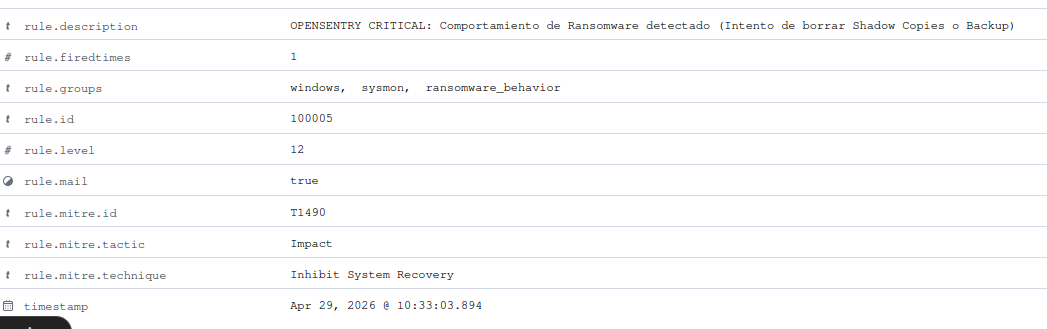
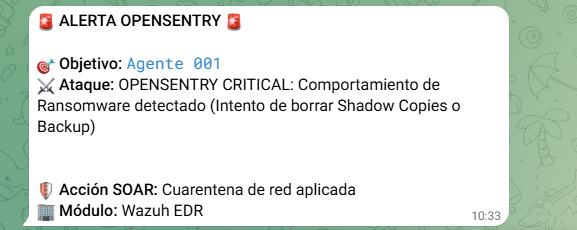
🛑 Dynamic Zero-Day Containment
Based on heuristic behavior to evade signatures. The engine detects malicious intent such as attempts to destroy Shadow Copies (typical of Ransomware - MITRE T1490). In the face of this lethal alert, the SOAR isolates the machine from the corporate network by real-time reconfiguration of its local firewall, blocking lateral movement while maintaining a secure line with the SOC for forensic investigation.